Security Tips for Banks to Protect Customers Through Better Online Banking System Security
A judge in Michigan may have set a precedent when he ruled in favor of a small business that sued Comerica Bank for reimbursement of $561,000 to recover money that hackers stole from the business' account as a result of a phishing scam. The judge believed that Comerica should have done more to safeguard its customer's assets. Unfortunately many banks and credit unions lack adequate security & notification features in their online banking systems to help customer protect themselves. But many of the tools and technologies that could have prevented Comerica's loss are available to all banks and at minimal cost.
I'm going to introduce you to four security features that can help customers proactively protect their assets and subsequently lower the loss risk to banks and credit unions. In 2011, every online banking system should, at a bare minimum, use these security features:
Strong Password or Pass Phrase Support
A common practice in online banking systems is to require passwords that meet certain criteria:
- Minimum length requirement (usually eight characters)
- Use upper and lower case letters
- Must include a number or special character
Passwords like this were ok in 2002, but today it's not enough for banking systems. Banks should be encouraging customers to use long pass phrases, such as "Turkey and stuFFing at 4599 Pet$ Road." Pass phrases like this are difficult to guess or crack using brute force password attacks.
While a few banks do support pass phrases, some online banking systems force users to use short passwords. Amazingly, some banks even still disallow special characters in passwords!
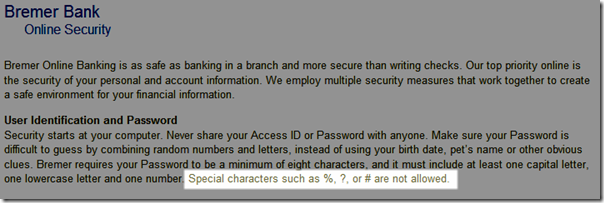
A surprising number of banks still prevent special characters in passwords
Banks and credit unions need to update their online banking systems to accept long, complex pass phrases. In addition, the systems need to enforce password expiration rules that require scheduled password changes and prevent re-use of old passwords.
Risk-Based Authentication
Many online banking systems today employ risk-based authentication (RBA) to prevent unauthorized access to customer accounts. A common RBA method uses a combination of challenge questions and security images. A weakness in many systems is the use of questions that hackers can easily answer with a minimal amount of research on Facebook, Geni.com or similar social sites.
For example, many systems ask, "What is your favorite color?" Even if the customer doesn't have a Facebook profile, this question has a small pool of common answers that a hacker can easily guess without knowing anything about the victim. When choosing RBA questions, the advice I offered in 2008 on best practices for choosing challenge questions is still relevant today.
The purpose of using a security image in online banking systems is to help a customer identify phishing sites. In theory a phishing site would not be able to show the correct security image for a specific user and therefore the user would not enter his credentials into the phishing site. One vulnerability of these systems is image harvest attacks. When the collection of available images is small, hackers can successfully harvest the images and execute a phishing scam.
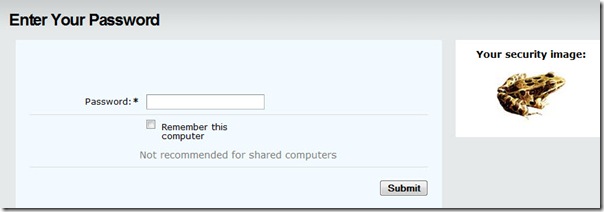
A common method of using a security image in an RBA process. If the user does not recognize the image, she should not enter her password.
To mitigate the risk of successful image harvest attacks, some RBA frameworks employ more sophisticated RBA image techniques. For example, MemberProtect has the ability to dynamically generate security images with embedded text to make each image unique to a specific customer. By adding an extra degree of protection like this to their online systems, a bank gives customers more options and further demonstrates to jurors how the bank took reasonable measures to protect customers.
A security image with an embedded security phrase
Multi-factor Authentication
In the Comerica Bank scenario, a multi-factor authentication system could have prevented the hackers from gaining access to the business accounts from which they transferred the money. One method of multi-factor authentication is RSA's SecurID keyfob system. SecurID uses small, electronic keyfobs that use an algorithm to generate a random pass code every 60 seconds. A user must enter this pass code in order to log into any system that the SecurID protects. Unfortunately, SecurID and similar systems are expensive to purchase and support due to the hardware and licensing costs, so few banks use them for customer accounts.
A newer and more cost effective solution uses something that many customers already have – a mobile phone or even landline telephone. Services like Authly will easily plug into an existing online banking system to generate one-time-use pass codes that are sent to a customer's mobile phone. To logon to online banking, the customer enters her username and password like normal, and then immediately she receives an eight character pass code on her phone via text message that she enters into the site to complete her login. The pass code can only be used once and expires shortly after the Authly system issues it. These types of systems make it very difficult for hackers to steal logon credentials and even if they do steal a code, it will have likely expired before the hacker can even use it.
Online banking systems should use tools like Authly for more than just logon. We recently implemented an online banking system that allowed customers to create domestic and international wires. To complete wires over a certain dollar amount, the customer had to enter a unique pass code for each wire. This system also made use of the pass codes for certain administration activities, such as adding users to certain privileged administrator-level roles within the online banking system. (Also, these systems put a daily cap on the number and total dollar amount of wires that a customer can perform in a day, which ads further protection.)
Real-time Out-of-Band Transaction Alerts
Thefts like the one in the Comerica case go undetected for days or weeks because most users do not check their banking activity on a daily basis. In the case of ACH and wire transfers, it's possible for a hacker to clean out a bank account in a matter of hours. When the account owner finally notices the loss days or weeks later and reports the theft, the funds are unrecoverable.
But banks and credit unions can easily provide customers with tools to monitor their accounts for unusual activity and thus give customers more control and responsibility in protecting their assets. Using services like Authly, or even simple email, a bank can allow a customer to configure notification rules on her accounts.
For example, Tina Marie could create a rule for the system to send her a text message anytime a transaction over $500 posts to her account. Many large banks and credit card issuers already have near real-time alerting systems integrated into their transactional systems, but small and mid-size banks and credit unions are lagging behind in this type of technology.
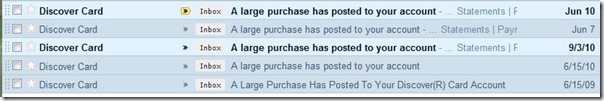
Real-time email or SMS text notification can help customers halt fraudulent transactions quickly
Better Security Adds Value for Customers
Implementing these types of security features will not create an impenetrable system. No internet facing system is 100% secure; however, by putting these four types of security mechanisms in place, banks and credit unions can better arm customers with the tools they need to protect their assets. In addition, the financial institutions will be in a better position to defend themselves when customers sue to recover losses from phishing and other scams.
If you're not sure your bank's security is up to par, then we should talk. We can help you identify weaknesses and recommend solutions to better protect your customers and their data.
Other Recent Blog Posts
Find this useful?
Want to receive our monthly tip to make your website easier to use and safer? No spam, just good advice. Signup!
Interests